What Is End-to-End Encryption (E2EE)?
End-to-End Encryption, or E2EE, is a way of protecting data so that only the sender and the intended recipient can read it. The data is encrypted on the sender’s device and is only decrypted later on the recipient’s device. Apart from these, no one in between, not even the service provider can read or access your content.
End-to-end encryption (E2EE) is different from standard encryption where data might be protected during transfer but still accessible to the platform storing it. Without E2EE, the platform can decrypt your data and is thus vulnerable to data breaches by hackers or third parties. With E2EE, the platform itself cannot decrypt your files or messages.
How Does End-to-End Encryption Really Work?
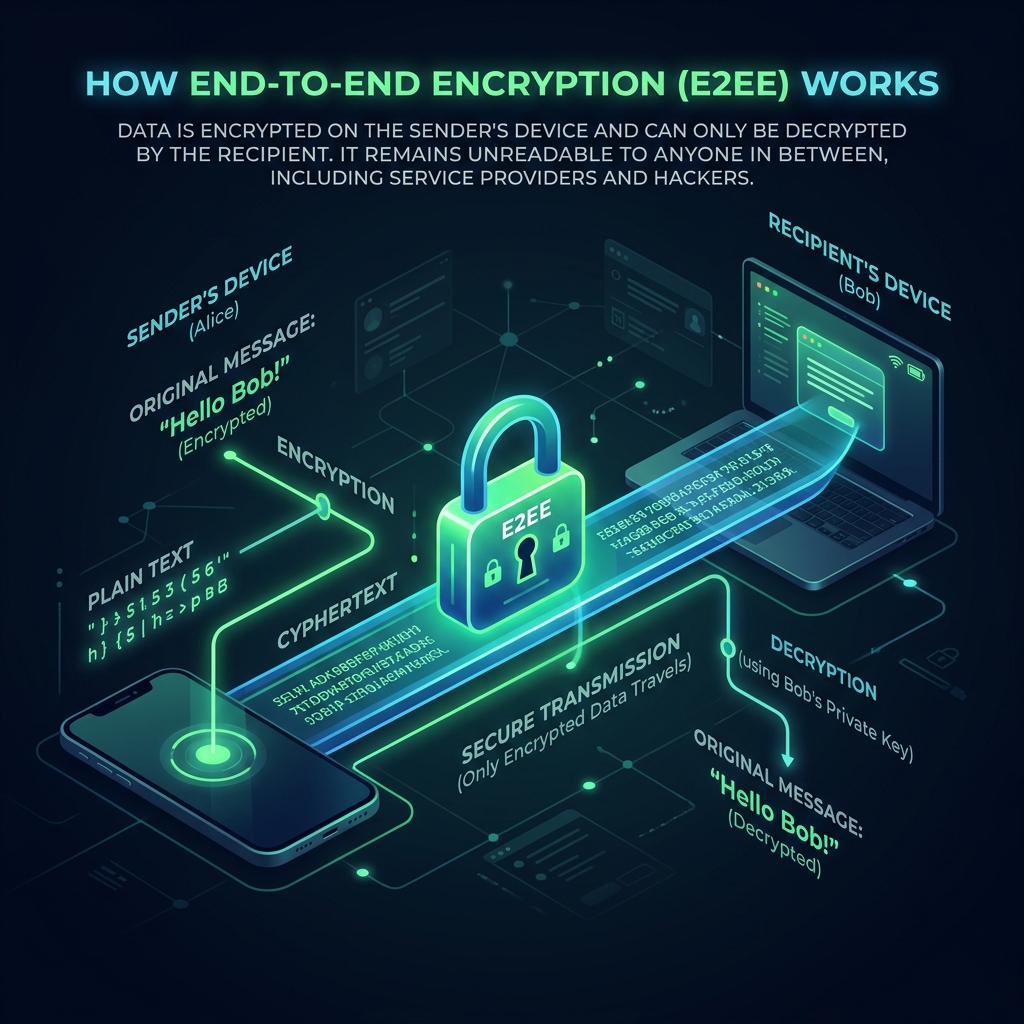
In E2EE, data is encrypted on the sender’s device using the recipient’s public key, converting it into unreadable ciphertext before it ever leaves the device. This encrypted data remains inaccessible because only the corresponding private key, stored securely on the recipient’s device can decrypt it.
Ciphertext can be understood as unreadable encrypted data produced when plaintext is processed using a cryptographic algorithm. This ensures that no one other than the sender and the intended recipient can read the content. Only those with the correct decryption key can convert it back into meaningful plaintext.
Real-Life Example End-to-End Encryption Example
You and your friend decide to share something confidential and write a note in a language that only the two of you understand.
Before sending it, you ensure that the content is translated into that secret language. Anyone who intercepts or tries to read it will only see meaningless symbols, since they don’t know how to interpret it.
Only your friend, who understands the same language, can read and make sense of it when they receive the note.

Standard Encryption vs End-to-End Encryption
Standard encryption protects data during transmission or while stored by converting it into unreadable form using cryptographic algorithms. The service provider typically manages the encryption keys, which means they can decrypt and access the data when needed.
Take a look at how standard encryption compares to end-to-end encryption (E2EE) -
| Feature | Standard Encryption (In-Transit / At-Rest) | End-to-End Encryption (E2EE) |
|---|---|---|
| Where encryption happens | During transmission (TLS) or on servers at rest | On the user’s device before transmission |
| Who can decrypt data | Service provider can decrypt (holds or controls keys) | Only sender and intended recipient |
| Key management | Keys are managed by the service provider | Private keys remain on user devices |
| Security against breaches | Data may be exposed if servers or keys are compromised | Data remains protected unless endpoints are compromised |
| Risk of Breaches | High | Low |
| True Privacy |
How DragBin’s End-to-End Encryption Works
Using DragBin, your files are encrypted on your device before upload and the keys are never visible to us. Your files remain encrypted in transit and at rest with complete metadata protection. This means that DragBin cannot see your passwords, files, filesnames or any other content.
Take a look at how DragBin’s end-to-end encryption works using the module below -
E2E Encryption Visualizer
This visualizer has two flows:
1. Backup: You encrypt a file locally. The session key is wrapped with YOUR public key so only you (after re-deriving your user key) can decrypt later.
2. Sharing: File encrypted once with a symmetric session key; that session key is wrapped with the RECIPIENT public key (hybrid encryption).
Manual mode (default): Each step is a scrollable 'card'. You must reach the bottom to unlock the Next button. This forces reading/learning pacing.
Auto mode: Cinematic slow-motion timeline. You can pause / resume and adjust speed.
Core principles: confidentiality (plaintext never leaves the client), integrity (AEAD), authenticity (verified recipient key), forward secrecy boundaries (fresh per-file session key).
The New Threat : Your Data Isn’t Safe
Just Because It’s Encrypted
In 1994, Peter Shor introduced Shor’s Algorithm, proving that a sufficiently powerful quantum computer could break widely used public key cryptography. What once seemed theoretical is now approaching reality and end-to-end encryption alone isn’t enough.
By the end of this decade, Google has indicated that practical quantum computers may arrive sooner than initially expected. Some experts even warn that quantum computers may arrive by 2029, meaning the window to secure our communications is closing faster than many anticipated. Due to this reason, banks, government organizations including the military and companies are already switching to quantum resistant encryption.
Attackers are already using a strategy called Harvest Now, Decrypt Later :
- Data is intercepted and stolen today
- Stored indefinitely in encrypted form
- Decrypted in the future once quantum capabilities mature
This means that your private files, videos, photos, government documents, bank details among other sensitive data can be exposed long after you’ve forgotten about them.
DragBin’s Quantum Resistant Encryption :
Security That Doesn’t Fail
To combat all threats from quantum computers, DragBin adds an additional layer of quantum resistant encryption to enhance client side, end-to-end encryption.
DragBin is built with post-quantum encryption, designed to withstand both current and future threats. We are open source and use quantum resistant encryption (ML-KEM + AES-256) to safeguard your data forever. Our zero knowledge architecture allows only you and you alone to access your data.
MLKEM Key Encapsulation
Quantum-resistant key encapsulation mechanism securing asymmetric key exchanges against future threats.
AES-256 Encryption
Industry-standard symmetric encryption with 256-bit keys. Your files are encrypted in transit and at rest.
Argon2 Key Derivation
Winner of the Password Hashing Competition. Securely derives keys from your password with high computational cost.
Who Needs End-to-End Encryption Apps?
Anyone dealing with sensitive or valuable data requires end-to-end encryption apps. This has become a necessity especially in the face of increasing cyberattacks and data breaches.
Creators & Video Editors
Protect unreleased content, footage and client work
Legal Teams
Secure contracts and confidential documents
Finance Professionals
Prevent exposure of financial records
Healthcare Providers
Protect patient data and compliance
Military and Defense
Confidential data, operations and instructions
Enterprises
Maintain control over organizational data
Agencies
Share work without risking leaks
Freelancers
Secure client deliverables and communication
What Are Some End-to-End Encryption Benefits?
For those looking beyond end-to-end encryption meaning and dwell into the benefits, this section is the perfect place to start. Unlike traditional models, end-to-end encryption removes server-side access entirely, thereby offering numerous benefits. This makes it one of the most reliable approaches for protecting sensitive data against breaches, surveillance and unauthorized access.
True Privacy
With end-to-end encryption, only the communicating endpoints can access the data, with no visibility for service providers. This ensures your data remains confidential and privacy is enforced with keys rather than depending on a server.
Data Ownership
Your data is yours and yours alone, retaining exclusive control over their encryption keys. This eliminates provider-level access, ensuring that ownership is not just conceptual but technically enforced through key possession.
Zero Trust Dependency
E2EE paves the way for minimum reliance infrastructure by ensuring that servers never handle decrypted data at any stage. Security does not depend on trusting the provider’s systems or policies, as access is cryptographically restricted to authorized endpoints only.
