What is Post Quantum Encryption?
Post quantum encryption (PQE) or post quantum cryptography are the cryptographic systems built to remain secure in the face of quantum computers. Unlike classical cryptography, PQE breaks old encryption and post quantum cryptography replaces it with stronger foundations.
Classical cryptography relies heavily on mathematical problems like integer factorization and discrete logarithms. These are hard for classical computers but quantum algorithms like 1994 Shor's algorithm can solve them efficiently.
Therefore, post quantum encryption creates difficult challenges with lattice based cryptography, multivariate polynomial cryptography and other advanced mathematical problems that are believed to remain hard even for quantum systems.
How Does Post Quantum Encryption Work?
To create challenges for quantum computers and protect our data, post quantum encryption changes how keys are generated, shared and protected. The reliance does not fall on vulnerable math rather systems like hash-based signatures and code-based cryptography among others.
Instead of RSA or elliptic curve cryptography, systems use algorithms like ML-KEM (based on lattice problems) to securely establish encryption keys. This approach revolves around the difficulty of finding the shortest vector in a high-dimensional lattice.
Moreover, many quantum resistant platforms like DragBin use hybrid cryptography, using both classical + post quantum cryptography algorithms. Larger key sizes like AES-256 are used to resist Grover's algorithm, which speeds up brute-force searches.
Visual Guide: Why Post-Quantum Cryptography Matters
Real Life Analogy of Post Quantum Cryptography
Max runs a company that manages invoices for over 10,000 clients, handling highly sensitive data like financial records and tax documents. He follows every best practice, storing data across multiple hard drives, maintaining on-site backups, and keeping a secure copy in the cloud. Then a flood destroys his office, wiping out all local storage, leaving only the cloud copy behind. Around the same time, the cloud provider suffers a breach, and attackers gain access to the stored data.
Max isn't immediately worried because everything is encrypted using systems like RSA and elliptic curves, which would take thousands of years to break with today's computers. But that sense of safety doesn't last, because in the future Lenny gets access to a quantum computer and unlocks that same data in minutes, while Joey, who quietly copied the encrypted files during the breach, simply waits and later decrypts everything at once. This is what's known as Harvest Now, Decrypt Later.
Quantum computers can try many possibilities at once, making old locks weak. Post-quantum encryption changes the lock itself : using problems that remain hard even for quantum machines.
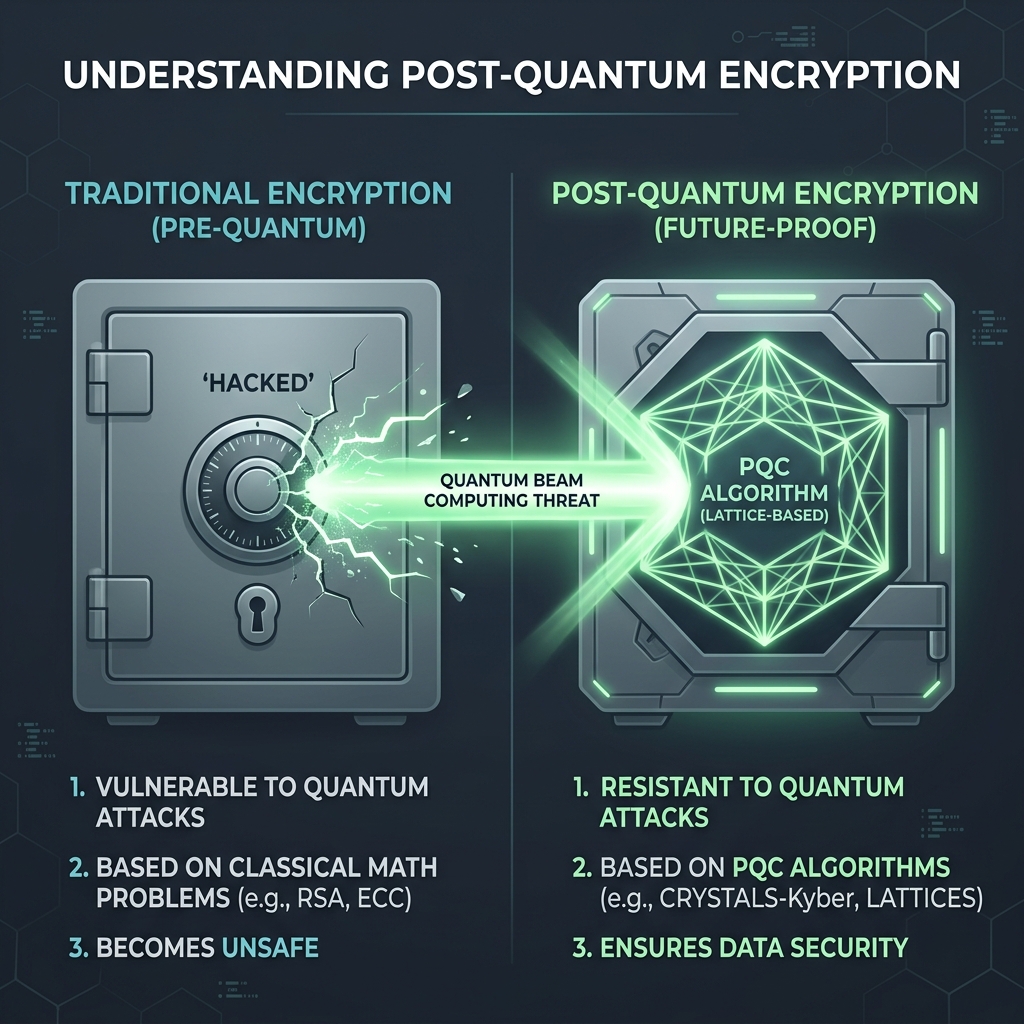
Classical Encryption vs Post Quantum Encryption
Numerous platforms use classical encryption today which is no longer a safe option with the threat of quantum computers. With advances in quantum computing and algorithms like Shor's Algorithm, the foundation of traditional encryption is starting to weaken.
Post-quantum encryption shifts the model entirely, take a look at the comparison table below -
| Feature | Classical Encryption | Post-Quantum Encryption |
|---|---|---|
| Security Basis | Relies on mathematical problems like factorization and discrete logs | Built on quantum-resistant problems like lattices and hash-based schemes |
| Quantum Vulnerability | Breakable with quantum algorithms like Shor's Algorithm | Designed to resist both classical and quantum attacks |
| Longevity | Secure today, vulnerable in the near future | Future-proof against emerging quantum capabilities |
| Attack Model | Assumes attackers use classical computing power | Assumes attackers may use quantum computers |
| Data Risk | Exposed to “harvest now, decrypt later” threats | Protects data even if intercepted and stored today |
Why Post Quantum Cryptography Has Become A Compulsion
With quantum computers expected to be operational by the end of this decade, post quantum encryption is not an upgrade but a necessity. Previously, the timeline was uncertain but now the direction is clear : switch to quantum resistant platforms immediately.
Hackers are utilizing the “Harvest Now, Decrypt Later” strategy to store your data and wait patiently till quantum computers come alive. They intend to decrypt it with future quantum computers, exposing your private files, confidential data and even national security secrets.
The PQC threat is active today and certain personal data has to be protected for decades. RSA and ECC will not survive large-scale quantum systems but post quantum cryptography will beat it. For this reason, governments, military departments and financial systems are already on the move towards quantum resistant systems.
How DragBin’s Quantum Resistant Encryption Works
DragBin is built with a post quantum encryption architecture from the ground up, aimed to secure your files forever. Your files are encrypted on your device before they ever reach the cloud, nobody (not even us) can see your files.
Encryption keys are secured using ML-KEM, a NIST-selected post quantum cryptography algorithm designed for quantum-resistant key exchange. Files themselves are encrypted using AES-256, which remains secure even in a post quantum world when properly implemented.
See how DragBin’s end-to-end, quantum-resistant encryption works using the module below -
E2E Encryption Visualizer
This visualizer has two flows:
1. Backup: You encrypt a file locally. The session key is wrapped with YOUR public key so only you (after re-deriving your user key) can decrypt later.
2. Sharing: File encrypted once with a symmetric session key; that session key is wrapped with the RECIPIENT public key (hybrid encryption).
Manual mode (default): Each step is a scrollable 'card'. You must reach the bottom to unlock the Next button. This forces reading/learning pacing.
Auto mode: Cinematic slow-motion timeline. You can pause / resume and adjust speed.
Core principles: confidentiality (plaintext never leaves the client), integrity (AEAD), authenticity (verified recipient key), forward secrecy boundaries (fresh per-file session key).
DragBin’s Zero Knowledge Security That Doesn’t Fail
We are completely open source, self hostable and offer a true zero knowledge security architecture. DragBin offers metadata protection and therefore cannot see your files, filenames, passwords or folders. With client side encryption, your keys never leave your device and private AI does not train on your data.
To sum it up, your data is not encrypted with quantum resistant encryption but is also unreadable to anyone except you.
End-to-End Encryption
Your files are encrypted on your device before they ever reach the cloud. We cannot access your keys.
Quantum Resistant
Secured using ML-KEM and AES-256 to ensure complete safety from future quantum computer attacks.
Zero Knowledge Architecture
True metadata protection. We cannot see your files, filenames, folders, or whom you share them with.
Open Source Code
Self hostable and fully transparent. Our cryptographic architecture is openly auditable by anyone.
Who Needs Quantum Resistant Platforms?
Legacy cloud storage platforms only offer end-to-end encryption and are not built for the future. DragBin ensures your data is protected today, tomorrow and in the future against all quantum computers. If your data has value beyond today and needs to be kept private for years to come, post quantum encryption is for you.
Post Quantum Encryption Benefits and Advantages
For those looking beyond post quantum cryptography algorithms and post quantum cryptography examples, here are some advantages below -
Quantum Resistant Security
Post-quantum cryptography is built on mathematical problems that remain hard for both classical and quantum computers, unlike RSA or ECC. This ensures your encryption does not become obsolete and is not vulnerable to Shor’s algorithm.
Protection from Retroactive Attacks
It prevents “harvest now, decrypt later” attacks by securing data against future decryption attempts using quantum machines. Even if encrypted data is intercepted and stored today, it remains unreadable indefinitely.
Stronger Cryptographic Foundations
Post-quantum systems rely on hard and advanced problems like lattice-based cryptography, which even quantum computers struggle to solve. This removes dependence on classical encryption methods that are already weakening under quantum research.
Long-Term Confidentiality
Sensitive data such as financial records, intellectual property, government data and personal files often need to remain secure for decades. Post-quantum encryption ensures that this data stays protected not just now, but throughout its entire lifecycle.
